Now is the time to make your website secure.
Last week at Enigma Conf 2016, some Google Chrome security engineers previewed the potential manifestation of a Chromium proposal which wants to have insecure content marked as such by default:
We, the Chrome Security Team, propose that user agents (UAs) gradually change their UX to display non-secure origins as affirmatively non-secure. We intend to devise and begin deploying a transition plan for Chrome in 2015.
The goal of this proposal is to more clearly display to users that HTTP provides no data security.
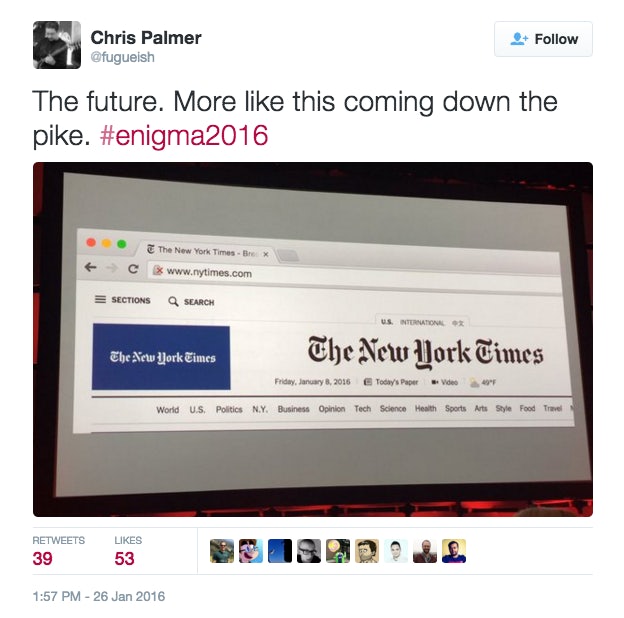
Chris Palmer (@fugueish on twitter) tweeted a now-removed photo of the demo, which I captured below demonstrating the potential UX soon to potentially be enabled by default for all HTTP content.
After a little research, we actually found out that this has been an option within the Chrome chrome://flags/ page for some time, titled “Mark non-secure origins as non-secure”.
We ran a little test on a local news website of our own to investigate the impact ourselves.
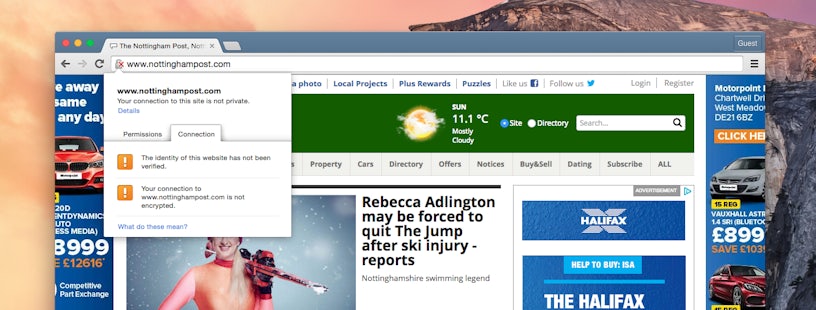
As you can see, the × appears over the permanent security padlock symbol – a change from the previous UX of having only the document icon there. The user is also explicitly warned about the lack of encryption on the website.
Is this a good idea?
Correctly configured end-to-end encryption of web traffic is the only true method of ensuring online communication cannot be eavesdropped upon. As a company of digital marketers, we have in recent years been drawn to SSL/TLS certificates for only a subset of the reasons a website may choose to ‘go secure’. Below are a few general benefits of having a secure website.
Higher level of trust and confidence in the website.
Few websites in 2016 will be just the typical ‘brochure website’ of the past. Many websites are now deeply integrated into CRM systems, eCommerce platforms and more. As a result, security of personal, contact and payment information is increasingly brought into question by users. Through using signed TLS certificates, websites are able to prove their authenticity, confidentiality and guarantees around the information they collect.
With increased levels of trust, typically conversion rates (form fills, ecommerce transactions) are higher as the user is put at ease.
Search Engine Optimisation benefit
Google has shown in the past that it is likely to prefer websites which display secure content over insecure content. As a result, many search marketers, including ourselves, were quick to certify our websites over a year ago. However, we’re yet to see significant step changes in how Google is handling this secure content.
To avoid mass disruption and now having allowed extra time for larger corporations to join the bandwagon, it’s our belief that Google will make more significant ranking algorithm changes in 2016 focussed around security signals.
What does this mean for marketers?
With this latest announcement at Enigma, Google’s sitting the other side of the fence to its usual position. By exposing insecure content, it’s pushing website owners to secure their assets. Their usual position is to pull people by using the carrot and stick method talking about potential SEO benefits.
As mentioned, few websites are secure so for marketers, step 1 is to audit online assets and procure the relevant certificates for all domains.
How to secure your website
The last year has seen many of the barriers to entry for obtaining HTTPS certificates lowered and this is great news for webmasters everywhere. In 2014 I reviewed the certificate options available but now the conversation has evolved somewhat as HTTPS certificates are now FREE!
For some time, CDN providers have been offering HTTPS for free, and last week Amazon Web Services (AWS) joined the movement through launching Certificate Manager to enable free certificate management and signing for AWS resources.
We’ve previously paid for HTTPS certificates as we wanted the extended validation bar when asking our potential customers for their contact information, but there are totally secure methods of receiving signed certificates for free, namely through letsencrypt.org. With this service, currently released in Beta, advanced system admins can generate and sign certificates themselves.
I hope this has been a useful post — please let me have your questions below!



